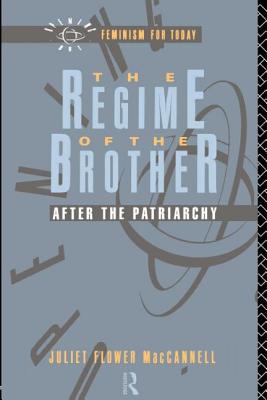
Polymorphic worm attacks are considered one of the top threats to Internet security. They can be used to delay networks, steal information, delete information, and launch flooding attacks against servers. This book supplies unprecedented coverage of how to generate automated signatures for unknown polymorphic worms. Describing attack detection approaches and automated signature generation systems, the book details the design of double-honeynet systems and the experimental investigation of these systems. It also discusses experimental implementation of signature-generation algorithms and discusses what we can expect in future developments.
Able to propagate quickly and change their payload with each infection, polymorphic worms have been able to evade even the most advanced intrusion detection systems (IDS). And, because zero-day worms require only seconds to launch flooding attacks on your servers, using traditional methods such as manually creating and storing signatures to defend against these threats is just too slow.
Bringing together critical knowledge and research on the subject, Automatic Defense Against Zero-day Polymorphic Worms in Communication Networks details a new approach for generating automated signatures for unknown polymorphic worms. It presents experimental results on a new method for polymorphic worm detection and examines experimental implementation of signature-generation algorithms and double-honeynet systems.
If you need some background, the book includes an overview of the fundamental terms and concepts in network security, including the various security models. Clearing up the misconceptions about the value of honeypots, it explains how they can be useful in securing your networks, and identifies open-source tools you can use to create your own honeypot. Theres also a chapter with references to helpful reading resources on automated signature generation systems.
The authors describe cutting-edge attack detection approaches and detail new algorithms to help you generate your own automated signatures for polymorphic worms. Explaining how to test the quality of your generated signatures, the text will help you develop the understanding required to effectively protect your communication networks. Coverage includes intrusion detection and prevention systems (IDPS), zero-day polymorphic worm collection methods, double-honeynet system configurations, and the implementation of double-honeynet architectures.
Get Automatic Defense Against Zero-day Polymorphic Worms in Communication Networks by at the best price and quality guranteed only at Werezi Africa largest book ecommerce store. The book was published by Taylor & Francis Ltd and it has pages. Enjoy Shopping Best Offers & Deals on books Online from Werezi - Receive at your doorstep - Fast Delivery - Secure mode of Payment
 Jacket, Women
Jacket, Women
 Woolend Jacket
Woolend Jacket
 Western denim
Western denim
 Mini Dresss
Mini Dresss
 Jacket, Women
Jacket, Women
 Woolend Jacket
Woolend Jacket
 Western denim
Western denim
 Mini Dresss
Mini Dresss
 Jacket, Women
Jacket, Women
 Woolend Jacket
Woolend Jacket
 Western denim
Western denim
 Mini Dresss
Mini Dresss
 Jacket, Women
Jacket, Women
 Woolend Jacket
Woolend Jacket
 Western denim
Western denim
 Mini Dresss
Mini Dresss
 Jacket, Women
Jacket, Women
 Woolend Jacket
Woolend Jacket
 Western denim
Western denim
 Mini Dresss
Mini Dresss